The UK Cyber Resilience Bill 2026 is the most significant overhaul of UK cyber legislation since the NIS Regulations in 2018. Currently progressing through Parliament with Royal Assent expected later this year, it expands regulatory scope, tightens incident reporting, and — for the first time — brings managed service providers under direct oversight.
Table of Contents
Signal Summary
The Cyber Security and Resilience (Network and Information Systems) Bill was introduced to Parliament in November 2025, completed second reading in January 2026, and passed committee stage by early March. It amends the Network and Information Systems Regulations 2018, expanding the range of organisations subject to formal cyber security obligations.
Managed service providers, data centres above 1MW rated IT load, and large load controllers now fall within scope. Incident reporting timelines tighten from 72 hours to 24 hours for initial notification, with a full report due within 72 hours. Royal Assent is expected later in 2026. Implementation will be phased, running through to 2028.
Why the UK Cyber Resilience Bill 2026 Is Structurally Significant
Three shifts distinguish this Bill from routine regulatory housekeeping.
Scope expansion. The original NIS Regulations covered operators of essential services — energy, transport, health, water, digital infrastructure. The Bill adds managed service providers, an estimated 900 to 1,100 firms, under direct ICO oversight. Data centres meeting defined capacity thresholds and large load controllers also come into scope. This is not a marginal widening. An entirely new category of commercial service provider is being placed under statutory cyber obligations for the first time.
Supply chain cascade. Regulated organisations will be required to assess and manage cyber risk across their suppliers. The practical reach extends well beyond the directly regulated entities. SMEs supplying services to larger businesses face new contractual requirements — security checks, incident response plans, evidence of baseline cyber hygiene. The growing problem of shadow AI in UK businesses compounds this exposure, creating risk vectors that many businesses have not yet mapped.
Enforcement teeth. Regulators gain the ability to issue compliance directions, impose financial penalties, and share information across enforcement authorities — including, in certain cases, with EU authorities under NIS2 alignment provisions. The Secretary of State gains new powers to direct specific entities in response to national security threats, without full parliamentary process. That last point is significant. It shifts cyber regulation from a slow-moving legislative exercise to a responsive enforcement mechanism.
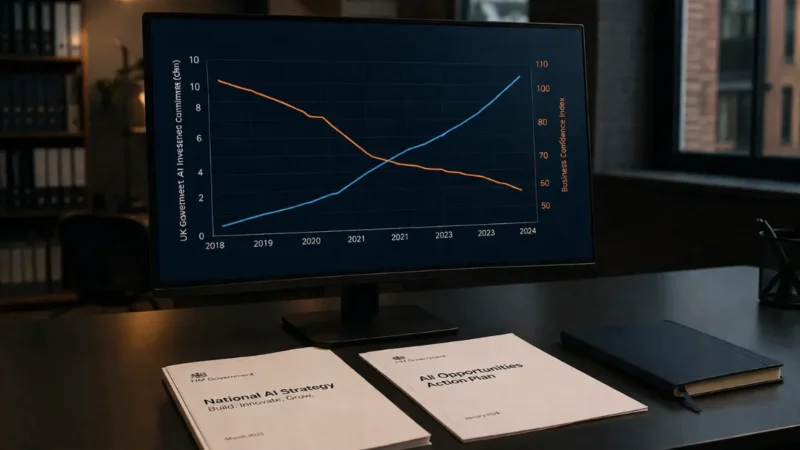
What Drove This
The numbers forced the issue. The NCSC’s latest Annual Review reported 204 nationally significant cyber incidents in the year to September 2025 — up from 89 the previous year. That is a 130% increase. Eighteen were classified as highly significant, a 50% rise for the third consecutive year. The Government responded by writing to all FTSE 350 boards, framing cyber resilience as a direct board-level responsibility.
The EU’s NIS2 Directive and DORA framework also played a role. Both raised the compliance baseline across Europe, and UK businesses operating cross-border or serving EU-regulated clients were already facing a growing compliance divergence. The Bill explicitly aims to bring UK cyber law closer to NIS2, reducing that friction.
Post-implementation reviews of the original NIS Regulations in 2020 and 2022 had already concluded that while the framework was having a positive impact, progress was too slow. The Bill is the overdue legislative response.
Implications for UK Businesses
Managed service providers face the most immediate impact. Firms providing outsourced IT management, cloud hosting, or security services will take on direct regulatory obligations — incident reporting, security standards aligned with the NCSC Cyber Assessment Framework, and potential cost recovery contributions to regulators. For an industry that has operated largely outside formal oversight, this is a fundamental change in operating conditions.
For SMEs, the impact is indirect but real. Supply chain obligations mean that larger clients will increasingly demand evidence of cyber security measures as a condition of doing business. Cyber Essentials certification, incident response plans, documented access controls — these shift from optional to expected. Businesses unable to demonstrate proportionate cyber governance risk being excluded from tenders altogether.
The cumulative regulatory burden matters here. The Employment Rights Act 2025 already reshaping UK startup operations is one example of concurrent compliance demands UK businesses are managing across employment law, data protection, and cyber security, each with distinct reporting requirements and enforcement mechanisms. The UK Cyber Resilience Bill 2026 adds another layer to an already demanding governance stack.
What to Watch Next
Royal Assent is expected later in 2026. Secondary legislation and statutory Codes of Practice will follow, and that is where the operational detail sits — specific security requirements, cost recovery mechanisms, the NCSC Cyber Assessment Framework’s formal adoption as a regulatory baseline.
Supply chain risk duties under the UK Cyber Resilience Bill 2026 will be enacted through secondary legislation. The precise obligations for vendors and suppliers are not yet codified, but the direction of travel is unambiguous. Waiting for the final text before acting is not a defensible position. The implementation runway to 2028 is shorter than it appears.
The widening governance gap around agentic AI in the UK is one of several parallel regulatory fronts. Autonomous AI systems, data protection enforcement, and digital market regulation are all advancing simultaneously. Businesses that treat each development in isolation will underestimate the total compliance effort required.
ObvioTech Assessment
The UK Cyber Resilience Bill 2026 is not aspirational policy. It is a structural reset of the UK’s cyber regulatory baseline, and its timing is deliberate.
The supply chain cascade is the element most businesses will underestimate. Direct regulation of MSPs matters, but the downstream effect on every business in their supply chain matters more. Procurement teams, contract managers, and operations directors — not just IT departments — need to understand what this Bill requires of them.
The 2028 implementation horizon sounds comfortable. It is not. Secondary legislation, internal policy development, supplier contract renegotiation, and Cyber Essentials certification take time. Businesses that begin preparation in 2026 will absorb the cost gradually. Those that wait will face a compressed timeline and a higher bill.
This is board-level. Not IT-level. The NCSC and the Government have made that explicit, and the Bill gives regulators the powers to enforce it.
Sources
UK Parliament — Cyber Security and Resilience (Network and Information Systems) Bill
GOV.UK — Cyber Security and Resilience Bill collection
NCSC — Annual Review 2025
House of Commons Library — Cyber Security and Resilience Bill research briefing
Taylor Wessing — UK Cyber Security and Resilience Bill: key considerations for technology businesses
Macfarlanes — Cyber Security and Resilience Bill progresses through Parliament